- 1. Security In The Workplace: Obligations, Standards, and Certifications
- DUERP
- Obligations
- Certifications
- 2. Fire Safety
- Tip 1: Check the certifications of its potential service providers:
- Tip 2: Determine the number and type of detectors needed according to the configuration of the premises:
- Tip 3: Check the standards:
- Tip 4:
- 3. Data Protection: The Essential Tools To Protect Your IT Assets
- 1 / Backups on external hard drives
- 2 / NAS:
- 3 / Backups on the company server
- 4 / Remote data backups
- 5 / Backup devices on appliances
Security Protection guide for businesses is a broad theme which includes in particular: compliance with the rules and obligations for the company, the fight against work accidents, fire safety and upgrading of premises, prevention of intrusions and burglaries, and flood prevention.
1. Security In The Workplace: Obligations, Standards, and Certifications
DUERP
The Single Document for Professional Risk Assessment (DUERP) consists of a mandatory document that assesses the risks to which the company’s employees are exposed. It is mandatory for any structure with at least 1 employee. It must be made available to employees to inform them of the risks involved. It must be updated regularly (once a year). DUERP identifies and classifies risks by seriousness.
Obligations
The employer is obliged to comply with standards relating to:
- Lighting: there must be sufficient light on the premises
- Heating
- Sanitation of premises and their ventilation
- Protection against noise (installation of anti-noise hoods on machines and distribution of hearing protection such as helmets and earplugs to employees)
- Signaling danger zones by putting up signs
- The layout of workstations, in particular, computer stations to avoid MSDs (musculoskeletal disorders), installation on computer screens for visual protection to limit eye fatigue and stress
- Sanitary facilities (sinks, showers, toilets) for employees to ensure their cleanliness
- Protection against tobacco with the establishment of areas specially dedicated to smokers
- First aid equipment thanks to the installation of medicine cabinets distributed in various places of the company
- Prevention and firefighting with the installation of fire extinguishers, armed fire valves, or even a sprinkler network
- Prevention of risks related to electrical installations or dangerous products with the provision of gloves and safety shoes as well as protective glasses
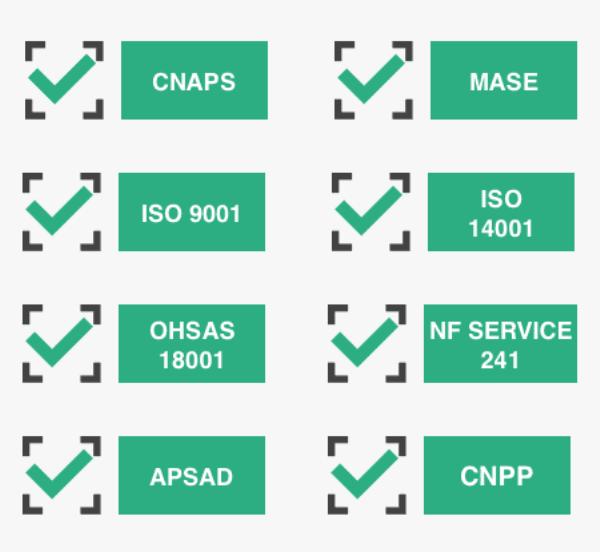
Certifications
By adhering to security standards and obtaining the appropriate certifications, you can secure your business, and reassure your employees, customers, and partners. If you are interested in making your life easier when attempting to attain any certification for your business, you can access Corning Data’s SAP staffing talent pool.
- CNAPS: The National Council for Private Security Activities has drawn up a guide providing an overview of the various standards existing in the private security sector.
- MASE: The Company Safety Improvement Manual identifies safety and environmental risks.
- ISO-9001: ISO-9001 is an international generalist standard issued on audit. ISO-9001 certification indicates that the company applies a management strategy in a “quality” approach, particularly in terms of risk analysis.
- ISO 14001: guarantees that the production and organization of the company meet environmental management requirements.
- AFAQ OHSAS 18001: The OHSAS 18001 certification is a management tool recognized throughout the world, which helps prevent accidents and reduce risks.
- NF SERVICE 241: certification which guarantees the rigor, transparency, and integrity of the activities of security companies.
- APSAD: APSAD certification attests to the quality of a fire safety, intrusion detection, or video surveillance system. It is valid for products as well as installation and maintenance services.
- CNPP: The National Center for Prevention and Protection is the body that issues APSAD certifications.
2. Fire Safety
The employer must take the necessary measures so that any outbreak of fire can be quickly brought under control to protect workers. If the employer is alone (without an employee), he is responsible for his safety and has no obligations regarding a fire safety system (SSI). It is nevertheless recommended to be equipped all the same to protect your life, your physical integrity, and your business (70% of companies experiencing a major disaster close in the following months).
If you have employees, the obligations regarding fire safety are as follows:
- Have at least one functional fire extinguisher with a minimum capacity of 6 liters per 200 m²
- Have at least one working fire extinguisher per floor
- Establishments open to the public (ERP) are subject to more stringent standards. Commercial space is considered an ERP. A register containing all technical verifications must be kept.
- Fire extinguishers: one device per level and every 200 to 300 m2 or every 150 m2 in industrial premises
- A fire alarm
- A fire safety system (SSI): this is all the equipment allowing fire detection, smoke extraction, compartmentalization (fire doors to prevent propagation), evacuation, automatic shutdown of certain installations, and automatic shutdown.
- An autonomous smoke alarm detector (DAAF) in establishments with residential use or on a case-by-case basis according to the requirements of insurers.
- In some cases: dry or wet columns, armed fire valves, automatic extinguishing systems
- A system of markings and signs to highlight evacuation exits and access paths.
- Security lights that can work in the event of a power cut.
In terms of building design, there are also specific safety rules for ERP:
- Construction of buildings with materials with suitable fire resistance
- Have at least 2 exits to allow rapid evacuation of occupants in the event of a disaster
- Have facades leading to the edge of the tracks to allow quick access for emergency services
- The premises must be arranged in such a way as to protect the occupants, in terms of distribution of rooms and isolation
- Any opening of an ERP must be validated beforehand by a security expert.
Some Tips:
Tip 1: Check the certifications of its potential service providers:
APSAD: The APSAD certification attests to the quality of a fire safety system. It is valid for both products and services.
Tip 2: Determine the number and type of detectors needed according to the configuration of the premises:
Your service provider will help you develop the best thought out and most secure Fire Safety System (SSI) possible, but you can already think about the number of detectors that you think are necessary, as well as their type:
- Carbon monoxide detectors: to be positioned near gas boilers to detect carbon monoxide, a deadly gas that is completely odorless
- Smoke detectors: it is recommended to provide one per 80 m² sectors, and one per floor. If you plan to have more than one, opt for interconnectable mains-plugged detectors that relay the signal, rather than independent battery-powered smoke detectors.
- · Heat detector: in kitchens, garages, or any other place where smoke and dust are common, a heat detector should be placed rather than a smoke detector. The heat detector triggers an alert when the temperature exceeds 52 ° C.
Tip 3: Check the standards:
- The detector packaging must be CE marked.
- The smoke detector must comply with European standard EN 14604.
- The carbon monoxide detector must comply with standard NF EN 50291.
Tip 4:
Notify your insurer: Inform your insurer (with which a contract covering fire damage in your premises has been concluded) that your premises are equipped with detectors.
3. Data Protection: The Essential Tools To Protect Your IT Assets
While digital technologies represent a strong development potential for companies, they can also be detrimental for very small and medium-sized businesses, underestimating the major cybersecurity risks. The need to protect its IT assets has become vital in order to ensure the sustainability of its business: by protecting its business data and by strengthening the cybersecurity of its information system. Companies must present the data security protection toolset which are useful tools for protecting business data on the computer, whether for preventive or curative purposes.
Preventive tools to counter common threats
Even if many companies still feel a little concerned by the risks associated with cybercrime , computer disasters today represent one of the major risks run by any professional organization. Keeping your corporate data out of prying eyes and protecting your data from the risk of loss or leakage should be your top priorities to ensure the continuity of your operations.
Next Generation Firewall (NGFW) to prevent intrusions
It will protect your computer system from recent sophisticated intrusions . It is a network security system that detects and blocks cyber attacks by intervening at the application level (detection of malware) and at the hardware level by applying security rules to the port or communication protocol through which your flows pass. digital.
Proxy to keep your data safe from prying eyes
Intermediary between your web browser and the Internet, a proxy server makes it possible to secure access to your data by hiding certain information in the case of anonymous proxies (IP address, operating system, web pages through which you went during your navigation …). Like a firewall, it boosts security by detecting malware and preventing outside computers from connecting to yours. The proxy also makes it possible to apply filtering rules according to your company’s IT security policy (blocking of sites according to a blacklist, sites deemed dangerous, unrelated to professional activity, legally or morally reprehensible …). One Authentication system to limit access to the external network is also possible, with the possibility of keeping logs (sites visited, pages viewed, users, etc.).
Antivirus against computer malware
If responsible use, in terms of browsing and the physical protection of your equipment against theft (via a complex password on each workstation for example), constitutes the first of the computer security precautions, antivirus protection is the basis for protecting your data from known viruses , Trojans and worms. This software makes it possible to spot malicious software identified at an early stage of distribution (malware) and to remedy it by deletion or quarantine. Read more about protecting data against malware attacks.
Antispam: beware of phishing emails
While most spam emails are simply unsolicited messages, often of an advertising nature, as unwanted as they invade your email, others are intentionally infected in order to harm their recipients.
Theft of confidential data, ransom demand… messaging is a privileged vector for carrying an attack. The first security measure is to never open the attachment of an unsolicited message, especially when the sender is not clearly identified. The spam is therefore an effective filtering device against messages from unknown transmitters. But beware, some messages are allegedly sent by your office colleagues or members of your address book whose identity has been usurped for the sole purpose of deceiving your vigilance…
Professional computer backup and the disaster recovery plan: to survive a disaster and guarantee the protection of your data. There are different kinds:
1 / Backups on external hard drives
Still widely used, which has the drawback of also being the victim of a disk crash in addition to being relatively time-consuming given the time spent manually copying the files. The backup and restore times are slow (USB port), the data is stored in clear on the disk and can therefore be used by any third party who would appropriate the medium. Finally, without file versioning, we cannot speak of professional backup! A corrupted or infected file with a cryptovirus will be saved as such and will overwrite the previous version which is surely perfectly healthy. Last point, when passing from one PC to another, the external hard drive is an excellent medium for the propagation of viruses within a network.
2 / NAS:
These hard drives connected to the corporate network are a low cost solution for many small business organizations. They can be offered in a Raid system to prevent the crash of one of the disks, the data being replicated on the second disk. Unfortunately, as with connected objects, their low cost makes them soft targets for cybercriminals. Some cybercriminal communities even concentrate their efforts on certain widely distributed material ( Synolocker being one of the most famous viruses).
3 / Backups on the company server
Which allow automatic and secure backups but which have the drawback of not surviving disasters leading to the deterioration or disappearance of the equipment storing the backed up data.
4 / Remote data backups
Which are relatively simple today and allow almost real-time backup (minimal risk of data loss). Disadvantage: the time to retrieve data from the server hosted in the cloud can be long (from a few hours to several days) because it depends on the volume of data saved and the speed of your internet connection.
No need to think about saving system images that are much too heavy but still very useful for a disaster recovery plan after a major disaster (cryptovirus, burglary, etc.). In addition, if for some reason you are without an internet connection, access to the data is not possible. We recommend that you ensure that the backed up data is hosted in the country where your business is registered in order to come under national jurisdiction. Otherwise, the confidentiality of your data is guaranteed only within the limits of the jurisdiction to which you will fall and in the event of a claim, you will go and plead and claim your damages abroad.
5 / Backup devices on appliances
The result of extensive hardware and software integration, these solutions offer many advantages. Fully automated, they do not require any internal IT resources or skills to operate.
It is therefore not surprising that they are acclaimed in small and medium-sized professional organizations or by multi-site companies.
They also offer the possibility of backing up data on site, on a box connected to the company’s local network, and of replicating the data on a remote site or in the cloud.
You thus benefit from the best of both worlds: quickly recoverable data and a true Disaster Recovery Plan from the system images stored on the box to deal with most disasters and remote storage, from which you can restore your data. data in the event of a disaster making your site permanently inaccessible.
The most advanced solutions also make it possible to save nomadic equipment (home office, roaming work) and to repatriate data to the box. In the event of theft of a laptop, you quickly reassemble an identical piece of equipment, without any loss of data!
For more information, see our article on turnkey data backup solutions.
In conclusion, the vulnerability issues to which companies are exposed today go well beyond computer viruses alone. They affect all the technologies used in a company’s information system. To protect yourself effectively, you must deploy an arsenal of professional preventive as well as curative defenses. These tools certainly have a price, your business continuity does not.
- 1. Security In The Workplace: Obligations, Standards, and Certifications
- DUERP
- Obligations
- Certifications
- 2. Fire Safety
- Tip 1: Check the certifications of its potential service providers:
- Tip 2: Determine the number and type of detectors needed according to the configuration of the premises:
- Tip 3: Check the standards:
- Tip 4:
- 3. Data Protection: The Essential Tools To Protect Your IT Assets
- 1 / Backups on external hard drives
- 2 / NAS:
- 3 / Backups on the company server
- 4 / Remote data backups
- 5 / Backup devices on appliances